macOS 下优雅的使用 Metasploit
macOS 下其实是可以直接安装原生的 Metasploit 的,这样很多攻击都可以在 macOS 下实现,基本上不需要打开 Kali Linux 虚拟机或者 Docker 了,很是方便,下面就简单记录下 mac 下 MSF 的安装。(不知不觉又水了一篇文章)
下载
| 版本 | 下载地址 |
|---|---|
| 最新的版本 | https://osx.metasploit.com/metasploitframework-latest.pkg |
| 最近10个版本安装 | https://osx.metasploit.com/ |
下载最新版本往往国内需要挂带来才可以很快的下载下来,这里建议配合proxychains4使用:
proxychains4 wget https://osx.metasploit.com/metasploitframework-latest.pkg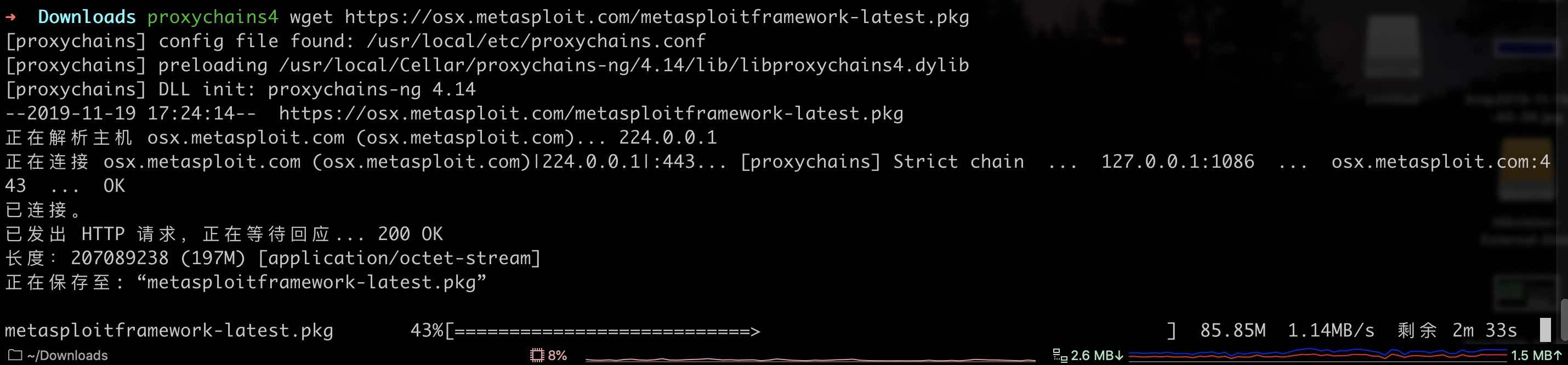
安装
安装很简单,双击metasploitframework-latest.pkg安装包,就可以安装了,macOS 下手动升级 Metasploit 版本国光这里建议也这样升级,比较方便省心。
配置
macOS 下 Metasploit 的可执行文件的位置为:/opt/metasploit-framework/bin
➜ tree /opt/metasploit-framework/bin
/opt/metasploit-framework/bin
├── msfbinscan
├── msfconsole
├── msfd
├── msfdb
├── msfelfscan
├── msfmachscan
├── msfpescan
├── msfremove
├── msfrop
├── msfrpc
├── msfrpcd
├── msfupdate
└── msfvenom方法一
下面手动创建一系列软链接方便我们启动:
ln -s /opt/metasploit-framework/bin/msfbinscan /usr/local/bin/msfbinscan
ln -s /opt/metasploit-framework/bin/msfconsole /usr/local/bin/msfconsole
ln -s /opt/metasploit-framework/bin/msfd /usr/local/bin/msfd
ln -s /opt/metasploit-framework/bin/msfdb /usr/local/bin/msfdb
ln -s /opt/metasploit-framework/bin/msfelfscan /usr/local/bin/msfelfscan
ln -s /opt/metasploit-framework/bin/msfmachscan /usr/local/bin/msfmachscan
ln -s /opt/metasploit-framework/bin/msfpescan /usr/local/bin/msfpescan
ln -s /opt/metasploit-framework/bin/msfremove /usr/local/bin/msfremove
ln -s /opt/metasploit-framework/bin/msfrop /usr/local/bin/msfrop
ln -s /opt/metasploit-framework/bin/msfrpc /usr/local/bin/msfrpc
ln -s /opt/metasploit-framework/bin/msfrpcd /usr/local/bin/msfrpcd
ln -s /opt/metasploit-framework/bin/msfupdate /usr/local/bin/msfupdate
ln -s /opt/metasploit-framework/bin/msfvenom /usr/local/bin/msfvenom方法二
如果嫌麻烦的话,还可以直接在zsh配置文件下配置 msf 路径的环境变量:
vim ~/.zshrc添加如下内容:
export PATH="$PATH:/opt/metasploit-framework/bin"然后刷新一下 zsh 即可正常使用 metasploit 的各种命令:
zsh使用
# 启动msf
$ msfconsole
** Welcome to Metasploit Framework Initial Setup **
Please answer a few questions to get started.
# 是否初始化一个数据库? y
Would you like to use and setup a new database (recommended)? y
Creating database at /Users/opposec/.msf4/db
Starting database at /Users/opposec/.msf4/db...success
Creating database users
Writing client authentication configuration file /Users/opposec/.msf4/db/pg_hba.conf
Stopping database at /Users/opposec/.msf4/db
Starting database at /Users/opposec/.msf4/db...success
Creating initial database schema
# 这里设置用户名和密码都msf
[?] Initial MSF web service account username? [opposec]: msf
[?] Initial MSF web service account password? (Leave blank for random password):
Generating SSL key and certificate for MSF web service
Attempting to start MSF web service...success
MSF web service started and online
Creating MSF web service user msf
############################################################
## MSF Web Service Credentials ##
## ##
## Please store these credentials securely. ##
## You will need them to connect to the webservice. ##
############################################################
MSF web service username: msf
MSF web service password: msf
MSF web service user API token: 2c8d9b7c229f47c710f1af9bbb720a96401fd3140001be4cf0b0d8234213a53f9c308b30bc78e491
MSF web service configuration complete
The web service has been configured as your default data service in msfconsole with the name "local-https-data-service"
If needed, manually reconnect to the data service in msfconsole using the command:
db_connect --token 2c8d9b7c229f47c710f1af9bbb720a96401fd3140001be4cf0b0d8234213a53f9c308b30bc78e491 --cert /Users/opposec/.msf4/msf-ws-cert.pem --skip-verify https://localhost:5443
The username and password are credentials for the API account:
https://localhost:5443/api/v1/auth/account
** Metasploit Framework Initial Setup Complete **
.;lxO0KXXXK0Oxl:.
,o0WMMMMMMMMMMMMMMMMMMKd,
'xNMMMMMMMMMMMMMMMMMMMMMMMMMWx,
:KMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMK:
.KMMMMMMMMMMMMMMMWNNNWMMMMMMMMMMMMMMMX,
lWMMMMMMMMMMMXd:.. ..;dKMMMMMMMMMMMMo
xMMMMMMMMMMWd. .oNMMMMMMMMMMk
oMMMMMMMMMMx. dMMMMMMMMMMx
.WMMMMMMMMM: :MMMMMMMMMM,
xMMMMMMMMMo lMMMMMMMMMO
NMMMMMMMMW ,cccccoMMMMMMMMMWlccccc;
MMMMMMMMMX ;KMMMMMMMMMMMMMMMMMMX:
NMMMMMMMMW. ;KMMMMMMMMMMMMMMX:
xMMMMMMMMMd ,0MMMMMMMMMMK;
.WMMMMMMMMMc 'OMMMMMM0,
lMMMMMMMMMMk. .kMMO'
dMMMMMMMMMMWd' ..
cWMMMMMMMMMMMNxc'. ##########
.0MMMMMMMMMMMMMMMMWc #+# #+#
;0MMMMMMMMMMMMMMMo. +:+
.dNMMMMMMMMMMMMo +#++:++#+
'oOWMMMMMMMMo +:+
.,cdkO0K; :+: :+:
:::::::+:
Metasploit
=[ metasploit v5.0.61-dev-56944c8364e66d13bcb077070ef4e44a73c987e6]
+ -- --=[ 1948 exploits - 1089 auxiliary - 334 post ]
+ -- --=[ 556 payloads - 45 encoders - 10 nops ]
+ -- --=[ 7 evasion ]
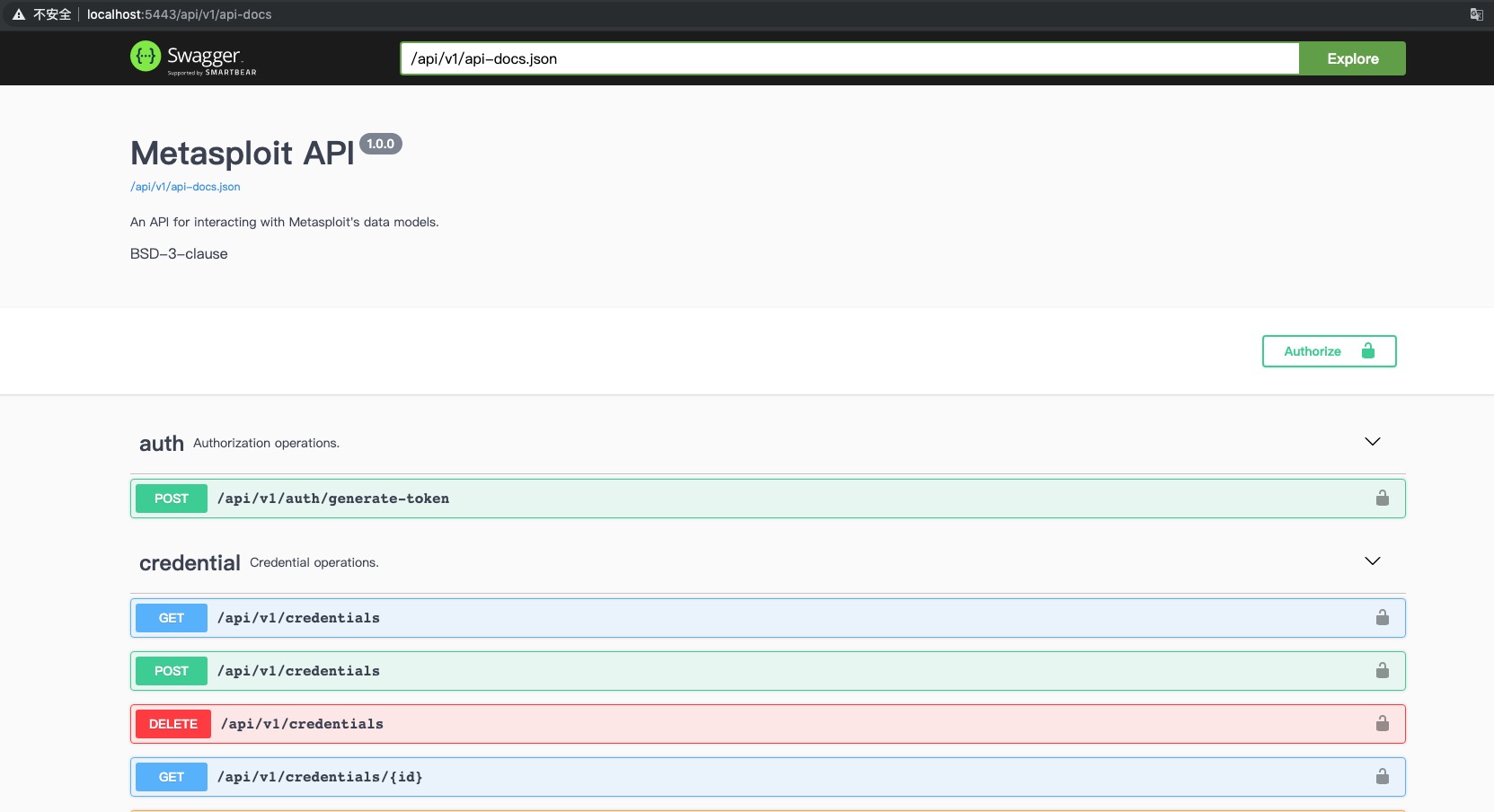
msf5 >macOS 安装的 Metasploit 自带 Web Servive,浏览器访问:https://localhost:5443/api/v1/auth/account 输入上面设置好的用户名和密码:
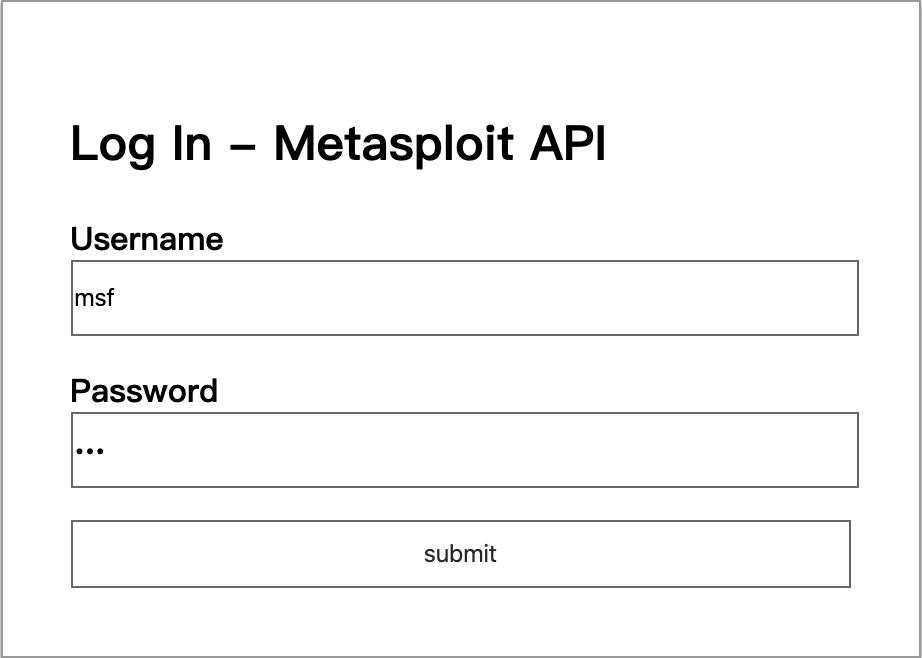
下面是大概的页面:
电脑如果后面重启的话,启动 Metasploit 的时候 再次输入用户名和密码即可成功启动:
➜ ~ msfconsole
[?] Would you like to delete your existing data and configurations?: n
Found a database at /Users/sqlsec/.msf4/db, checking to see if it is started
Starting database at /Users/sqlsec/.msf4/db...success
[?] Initial MSF web service account username? [sqlsec]: msf
[?] Initial MSF web service account password? (Leave blank for random password):支持一下
本文可能实际上也没有啥技术含量,但是写起来还是比较浪费时间的,在这个喧嚣浮躁的时代,个人博客越来越没有人看了,写博客感觉一直是用爱发电的状态。如果你恰巧财力雄厚,感觉本文对你有所帮助的话,可以考虑打赏一下本文,用以维持高昂的服务器运营费用(域名费用、服务器费用、CDN费用等)
微信
 |
支付宝
 |
没想到文章加入打赏列表没几天 就有热心网友打赏了 于是国光我用 Bootstrap 重写了一个页面用以感谢支持我的朋友,详情请看 打赏列表 | 国光